How to accept SSH host keys automatically on Linux
Last updated on August 14, 2020 by Dan Nanni
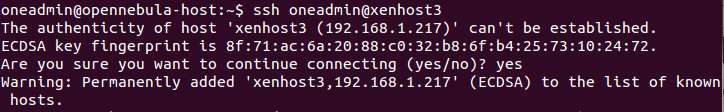
When you connect to an SSH server for the first time, you will be shown a fingerprint, a hash of its full host key, and asked to confirm its validity, and accept the host key. Once confirmed, the host key will be added to ~/.ssh/known_hosts file. However, in a controlled environment where the authenticity of SSH hosts is already known (e.g., local VMs), you may want to automatically accept a new host key without checking. This will be useful when you ssh/scp in a non-interactive batch processing script.
In this post, I will describe how to automatically accept SSH host keys on Linux.
The ssh command allows you to use -oStrictHostKeyChecking=[yes|no] command line option to enable or disable ssh host key checking. To ssh without strict host key checking, run the following.
$ ssh -oStrictHostKeyChecking=no user@remote_host
In this case, you will not be prompted to accept a host key. Note that you may still see the following warning message if the host key does not match with a previously added host key of the same host.
WARNING: REMOTE HOST IDENTIFICATION HAS CHANGED
If you don't want any such warning, you can use -oUserKnownHostsFile=/dev/null option, which makes ssh not use ~/.ssh/known_hosts, and so makes such warnings disappear.
$ ssh -oStrictHostKeyChecking=no -oUserKnownHostsFile=/dev/null user@remote_host
If you want to disable strict host key checking permanently in SSH, you can use a SSH configuration file (i.e., ~/.ssh/config or /etc/ssh/ssh_config). In this case, you can selectively disable SSH host key checking for particular hosts. For example, add the following to either ~/.ssh/config or /etc/ssh/ssh_config.
To disable host key checking for a particular host (e.g., remote_host.com):
Host remote_host.com
StrictHostKeyChecking no
To turn off host key checking for all hosts you connect to:
Host *
StrictHostKeyChecking no
To avoid host key verification, and not use known_hosts file for 192.168.1.* subnet:
Host 192.168.0.*
StrictHostKeyChecking no
UserKnownHostsFile=/dev/null
Support Xmodulo
This website is made possible by minimal ads and your gracious donation via PayPal or credit card
Please note that this article is published by Xmodulo.com under a Creative Commons Attribution-ShareAlike 3.0 Unported License. If you would like to use the whole or any part of this article, you need to cite this web page at Xmodulo.com as the original source.
Xmodulo © 2021 ‒ About ‒ Write for Us ‒ Feed ‒ Powered by DigitalOcean

