How to create an encrypted zip file on Linux
Last updated on September 22, 2020 by Dan Nanni
Suppose you want to create a zip archive, but with password protection, so that whoever tries to uncompress the zip file must know the right password. On Linux, there are several ways to encrypt and password protect a zip file.
In this tutorial, I will describe how to create an encrypted zip file on Linux.
Method One: zip
The zip command line tool provides an encryption option. The encryption algorithm used by zip command is PKZIP stream cipher. The PKZIP algorithm is known to be insecure. Also, the fact that the password is typed and shown in plain text makes it even more vulnerable.
To create an encrypted zip file with zip:
$ zip --password MY_SECRET secure.zip doc.pdf doc2.pdf doc3.pdf
To uncompress a zip file that is encrypted with zip command:
$ unzip secure.zip
Archive: secure.zip [secure.zip] doc.pdf password:
Method Two: 7z
7z file archiver can produce zip-format archives with more secure encryption scheme. 7z archiver supports AES-256 encryption algorithm with SHA-256 hash algorithm based key generation.
To create an encrypted zip file with 7z archiver:
$ 7za a -tzip -pMY_SECRET -mem=AES256 secure.zip doc.pdf doc2.pdf doc3.pdf
To uncompress a zip file that is encrypted with 7za command:
$ 7za e secure.zip
7-Zip (A) [64] 9.20 Copyright (c) 1999-2010 Igor Pavlov 2010-11-18 p7zip Version 9.20 (locale=en_US.UTF-8,Utf16=on,HugeFiles=on,8 CPUs) Processing archive: secure.zip Extracting doc.pdf Enter password (will not be echoed) :
Method Three: GnuPG
Another way to create a secure zip archive is to use GnuPG's symmetric key encryption.
To create an encrypted compressed tar archive with GnuPG:
$ tar czvpf - doc.pdf doc2.pdf doc3.pdf | gpg --symmetric --cipher-algo aes256 -o secure.tar.gz.gpg
To uncompress an archive file encrypted with GnuPG:
$ gpg -d secure.tar.gz.gpg | tar xzvf -
Method Four: Nautilus File Manager
If you use Nautilus file manager on your Linux desktop, you can use Nautilus GUI to create a password-protected zip file easily.
First, highlight a set of files to include in the archive. Then right-click them, and choose Compression option.
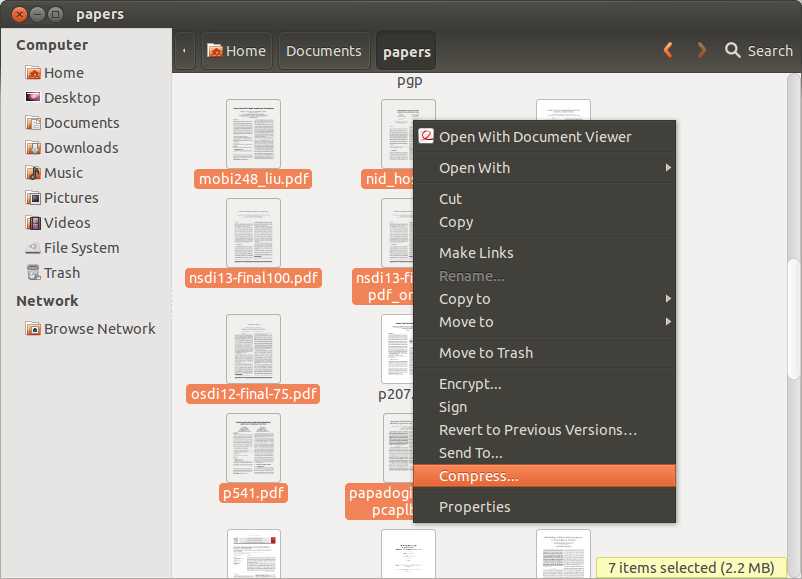
Fill in the archive file name, and select .zip suffix (or .7z if you have installed 7z archiver). Click on Other Options and fill in your password. Underneath Nautilus, it will use zip command to create an encrypted archive.

Support Xmodulo
This website is made possible by minimal ads and your gracious donation via PayPal or credit card
Please note that this article is published by Xmodulo.com under a Creative Commons Attribution-ShareAlike 3.0 Unported License. If you would like to use the whole or any part of this article, you need to cite this web page at Xmodulo.com as the original source.
Xmodulo © 2021 ‒ About ‒ Write for Us ‒ Feed ‒ Powered by DigitalOcean

