How to enable SSH login without entering password
Last updated on November 25, 2020 by Dan Nanni
If you are accessing a remote server frequently, it is convenient for you to be able to SSH to the remote host without entering an SSH password. Passwordless SSH login is even more useful when you are using SSH for non-interactive purposes, for example, for filesystem mount, offsite backup, remote file sync, etc. Also, many distributed systems or cloud orchestration layers (e.g., OpenStack) leverage password-less SSH authentication to control remote compute nodes.
If you want to log in to a remote SSH server without entering an SSH password, you can instead use key-based authentication, where you install your public key on a remote server a priori, and then log in to the server by presenting your private key as an authentication key.
Enable Passwordless SSH Login with Key Authentication
Here is how to enable SSH login without entering an SSH password.
Assume that you are a user account alice on host1, and wish to ssh to host2 as user bob, without entering the bob's password.
First, you need to be logged in as user alice on host1.
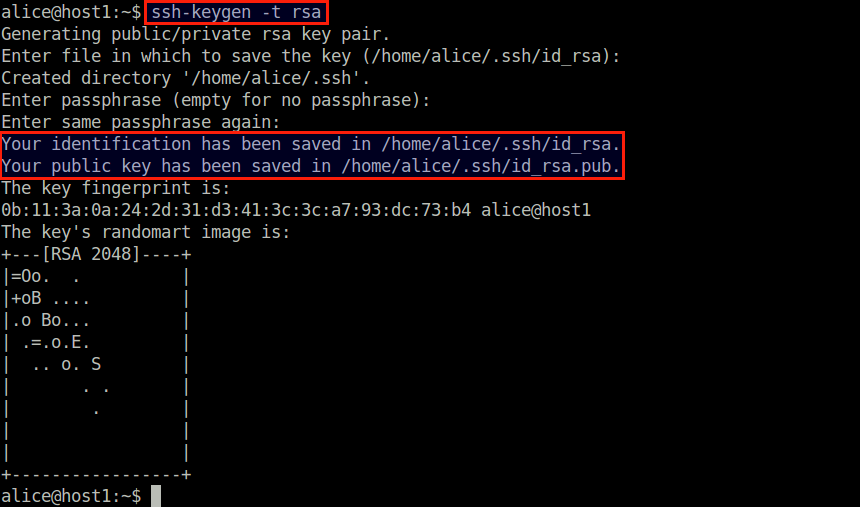
Generate a public/private RSA key pair by using ssh-keygen command.
$ ssh-keygen -t rsa
The generated key pair (id_rsa and id_rsa.pub) will be stored in ~/.ssh directory of alice user.
Next, you need to install the generated public key (~/.ssh/id_rsa.pub) of alice to the remote server host2 under the bob account. This can be achieved by ssh-copy-id command as follows.
$ ssh-copy-id -i ~/.ssh/id_rsa.pub bob@host2
You will then be asked to enter the bob's password. Once you enter the bob's password, the alice's public key will be installed on the remote server host2.
From this point on, you no longer need to type in the bob's password when you SSH from alice@host1 to bob@host2.
Specify a Private Key to Use
If you have multiple public/private key pairs to use for different SSH servers, you can specify that information in ~/.ssh/config file, so that a correct private key is used automatically without you having to use -i option. Refer to this tutorial for more information.
Troubleshooting
1. Authentication refused error
Symptom: You are still asked for an SSH password even after enabling key authentication. In this case, check for system logs (e.g., /var/log/secure) to see if you see something like the following.
Authentication refused: bad ownership or modes for file /home/aliceB/.ssh/authorized_keys
In this case, failure of key authentication is due to the fact that the permission or ownership ~/.ssh/authorized_keys file is not correct. Typically this error can happen if ~/.ssh/authorized_keys is read accessible to anyone but yourself. To fix this problem, change the file permission as follows.
$ chmod 700 ~/.ssh/authorized_keys
2. Connection closed error
Symptom: You fail to connect to a remote SSH server with "Connection closed by X.X.X.X." On the SSH server side, you see the following error log.
sshd error: Could not load host key: /etc/ssh/ssh_host_rsa_key
The problem is due to the corrupted or missing private keys on the SSH server side. To solve this problem, you need to re-generate the SSH host keys.
Support Xmodulo
This website is made possible by minimal ads and your gracious donation via PayPal or credit card
Please note that this article is published by Xmodulo.com under a Creative Commons Attribution-ShareAlike 3.0 Unported License. If you would like to use the whole or any part of this article, you need to cite this web page at Xmodulo.com as the original source.
Xmodulo © 2021 ‒ About ‒ Write for Us ‒ Feed ‒ Powered by DigitalOcean

