How to measure network latency, packet loss and jitter on Linux
Last updated on September 26, 2020 by Dan Nanni
If you experience quality issues on your network, you may want to look into monitoring your network to draw any clues about the issues. A tool called SmokePing comes handy in this case. SmokePing is one of the best network latency visualization tools available on Linux.
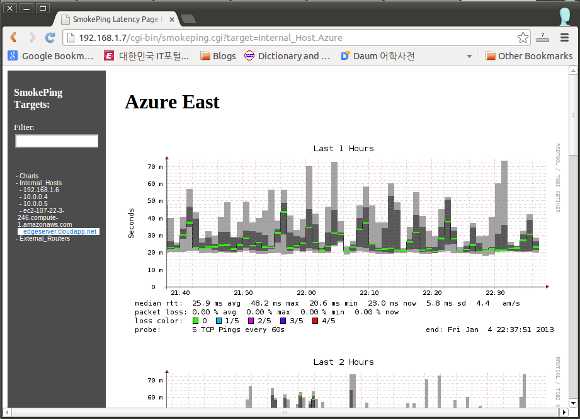
For latency visualization, SmokePing relies on a list of other probing utilities (e.g., fping, tcpping, etc.) to measure network latencies. The individual measurements generated by these probing utilities are then stored locally as time-series data. SmokePing use this data to visualize packet latency, loss and jitter over a time period.
In this tutorial, I will describe how to measure network latency, packet loss and jitter with SmokePing.
If SELinux is enabled on your system, SmokePing may not run properly. So make sure to disable SELinux on your system. To disable SELinux, edit /etc/selinux/config as follows, and reboot.
$ sudo vi /etc/selinux/config
SELINUX=disable
Install SmokePing on Linux
To install SmokePing on Ubuntu or Debian, do the following:
$ sudo aptitude update $ sudo aptitude install smokeping curl libauthen-radius-perl libnet-ldap-perl libnet-dns-perl libio-socket-ssl-perl libnet-telnet-perl libsocket6-perl libio-socket-inet6-perl apache2 sendmail
To install SmokePing on Fedora, run:
$ sudo yum install smokeping
Configure SmokePing
Once you have installed SmokePing, configure it as follows.
$ sudo vi /etc/smokeping/config.d/General
cgiurl = http://ip_address_of_your_host/cgi-bin/smokeping.cgi
By default, SmokePing will measure network latencies for local host, by using fping. You can customize this default settings as you wish (e.g., add additional probing destinations, change probing tools, etc). Read on to learn how to customize SmokePing settings.
1. Customize Probing Tools
To configure probing tools to use in SmokePing, edit the following.
$ sudo vi /etc/smokeping/config.d/Probes
+ FPing binary = /usr/bin/fping offset = 50% step = 60 timeout = 10 pings = 5 + TCPPing binary = /usr/bin/tcpping forks = 5 offset = 50% step = 60 timeout = 10 pings = 5
In the above example, I define two probing tools: fping and tcpping. The former uses ICMP packets to measure latencies, while the latter uses TCP packets. tcpping is useful when a destination host blocks ICMP packets.
binary: path for a given probing tool.fork: how many processes to use for probing.offset: how varied multiple concurrent probes are in terms of their launch time within a given time interval.step: duration of time interval (in seconds) for probing.timeout: timeout value to be used in a given probing tool.pings: how many pings should be sent in each time interval.
2. Customize Probing Destinations
To configure a list of destination hosts to probe, edit the following.
$ sudo vi /etc/smokeping/config.d/Targets
probe = FPing menu = Latency title = Latency Measurement remark = SmokePing Latency Test. + Internal_Host menu = Internal_Hosts title = Cloud Latency Measurements ++ Home title = Home host = 192.168.1.6 ++ Verizon_FIOS title = Verizon FIOS host = 10.0.0.4 ++ Optimum title = Optimum Online host = 10.0.0.5 ++ EC2 title = EC2 East host = ec2-102-22-3-146.compute-1.amazonaws.com ++ Azure title = Azure East host = edgesrver.cloudapp.net + External_Router menu = External_Routers title = Cloud Latency Measurements probe = TCPPing ++ Verizon_DSL title = Verizon DSL probe = TCPPing host = 72.52.53.66
You can customize the above file as you want. For each probing target (under ++), you can define a custom probing tool to use (e.g., probe = TCPPing). For a complete list of probing tools that are compatible with SmokePing, refer to the official source. Note that you will need to install any necessary probing tools separately if you decide to use them.
Whenever you change SmokePing configuration, be sure to restart SmokePing as follows.
On Ubuntu or Debian:
$ sudo /etc/init.d/smokeping restart
On Fedora:
$ sudo service smokeping restart
SmokePing may fail to restart if there are existing measurements collected based on the previous configuration, and the updated configuration is not compatible with existing measurements. In that case, you will need to remove previously collected measurements (located in /var/lib/smokeping) in order to be able to restart SmokePing.
You can browse latency measurements visualized by SmokePing at http://<ip-address-of-your-host>/cgi-bin/smokeping.cgi. This web page will automatically be refreshed as latency measurements are accumulated.
Support Xmodulo
This website is made possible by minimal ads and your gracious donation via PayPal or credit card
Please note that this article is published by Xmodulo.com under a Creative Commons Attribution-ShareAlike 3.0 Unported License. If you would like to use the whole or any part of this article, you need to cite this web page at Xmodulo.com as the original source.
Xmodulo © 2021 ‒ About ‒ Write for Us ‒ Feed ‒ Powered by DigitalOcean

